of Cyber Attacks
Introduction
Today’s business user faces an increasing number of cyber attacks from email, on-line websites, web portals and other Internet based threats. This guide gives an overview of our best practices and overview of common threats and solutions suitable to small and medium business enterprise (SME) users. Whether you are the business own or a day-to-day user of IT systems, we hope there is something here for you all and of course if you need any help in this area we would be delighted to assist you.
About Charlton Networks
Charlton Networks provide a complete set of Business IT services for Small and Medium Businesses (SME). This includes working with business owners and senior management teams, assisting individual users and managing day-to-day ICT operations. By working at all levels across your business, we bring strategic and operational improvement aimed at reducing the IT costs, increasing business productivity and removing the ‘headache’ of dealing with multiple suppliers.
Key services include:
- Board Level IT and IT Strategy
- Bespoke IT Systems and Custom Software
- Flexible IT Support
- Essential Cyber-Protection
- One-Stop-Shop for SME IT Needs
Our 22-year heritage means we understand the specific needs of many business sectors and our varied client list includes private companies, manufacturing, local government, education and not-for-profit. Testimonials and case studies of our work is available upon request.
Our aim is to provide the very best and most comprehensive IT support and installation services. We achieve this by using our own in-house team of dedicated IT professionals to deliver cost effective IT systems that are consistently reliable, providing our clients with both peace of mind and value for money.
Cyber-Security Threats & Cyber Attacks
This is a list of common threats and how they work.
Viruses
This is typically a piece of computer code that is able to copy itself and replicate itself around a group of computers, across the Internet, typically transported by email or as part of a file installation on a removable medium such as a USB drive. Viruses are generally malicious and corrupt data and system file, rending the computer systems unusable.
Malware
Malware is malicious software specifically designed to disrupt, damage, or gain unauthorized access to a computer system. Designed to disrupting the normal operation of your IT devices, computers and file servers and typically generated via accessing a rouge web sites or by installing software that has been ‘infected’ (viruses, worms, Trojans, etc.).
Ransomware
Ransomware is a form of Malware (malicious software) designed to block access to a computer system until a sum of money is paid. This is achieved by encrypting data with a ‘key’ (password) that is only known to the hackers, which they then attempt to sell to the company so that they can decrypt their own data.
Phishing
This is a type of computer fraud that tries to trick a user into revealing their confidential and private information. This can include passwords, date of birth, address or bank details and gaining these by posing as a legitimate request for information. This is now seen frequently in e-mails where attempts are made to coax recipients into revealing this private data. Increasingly these attacks are ever more sophisticated, posing as bank and other reputable websites to trick users in to giving up this private data.
Device Vulnerability
The rise in the number of networked devices, such as PC, tablets, phones, CCTV, storage and backup (also known as IoT [Internet of Things]) means that almost everything is now becoming Internet connected. Every device has some form of ‘vulnerability’ and as these become known, software updates and patches are released to protect these devices. Identifying these known threats means constantly reviewing the update status of devices to ensure the preparedness of your devices, systems & infrastructure.
Data Leakage / Insider Threats
As your company grows and your staff numbers increase the potential for some ‘unauthorized’ transfer of company information also increases. Data leakage at it’s simplest can be done simply by a user remembering what they have seen. Perhaps more significantly, the physical or logical copying and removal of data can be achieved via things like removeable disks or email attachments of critical data, such as client lists.
Weak Passwords
An organisation called SplashData has published its annual list of the most commonly used passwords of the year. The top three are 123456, password and 123456789. The top two are unchanged since last year. What does your organisation do to make sure that your passwords are hard to guess and, like toothbrushes, never shared? “Ew, don’t even go there.” According to some 2017 training by the PCI Security Standard Council, the lovely people who work to keep our payment card data safe, the password bigmac can be cracked in 0.077 seconds by a brute force attack program whereas leB1gMac takes 14 hours and M1gMac&fries would take 344,000 years. There are faster machines around now, but the core truth still stands: train the people and enforce better passwords using system controls.
Denial of Service Attack (DOS) & Distributed Denial of Service (DDOS):
DoS & DDoS attacks aim to make publicly facing webservices system unusable. Typically, network traffic is generated by the hacker from a single (DoS) or multiple-locations (DDoS) that flood the available Internet connection or web resources so that one can use the service.
Cyber-Security User Best Practice
Introduction
“Tell me something I don’t know” grumbled the owner of an award-winning business. “Please be more imaginative than “You need to back up your email.”
That’s a fair point but this business still didn’t have a plan to cope with an email problem; they simply believed it would never happen to them. People know that five veg a day, cardio vascular exercise and smiling are all good practices, but not enough people do even one of those, let alone all three. You probably know about these cyber threats but have not got around to managing them just yet. The Cyber Breaches Security Survey 2018 published by the Department for Digital, Culture, Media and Sport stated that only three in ten businesses have a formal cyber security policy.
Here are some useful guidance, tips and best practice on improving your cyber-security through your daily use of IT systems and on-line working.
Email Attachments
Try not open any attachments directly from email, even if you are convinced of the source. Saving it to your desktop and opening it from there will ensure that anti-virus fully checks the attachment and you are not initiating an action that may have unknown consequences.
Email Links
Do not click on any embedded links in an email. Rather, right-click and ‘copy URL’ in to your browser. Paste this in to your browser and look at the source before proceeding, making sure this is not some spam site set-up to capture your credentials.
Password Resets
Don’t reset your passwords direct from an email link, but less you have actioned the reset. Rather, go to the source site. i.e. Microsoft and login manually and change as prompted, this avoids the risk of phishing emails designed to capture your passwords and other personal data.
Reporting Cyber-Issues
If you suspect anything as suspicious, call your IT department or outsourced IT providers immediately. Don’t rely of sending an email, especially if you are concerned about an email! Emails are frequently filtered & junk / spam emails removed, so best be safe and speak to a human, explain the concerns and always ask for help.
Try a Test Restore
Most people understand data backup, few people ever restore a file unless they have a problem. When was the last time you restored a file and checked that you could use it? How far back in time can you go?
Better still, when was the last time your company did a full restore of all your data? It is good to know what you would have to do and to realise how long it could take. If a ransomware attack hit your data, how would you respond?
Replace out dated Hardware and Software
Software and hardware, like premiership football teams, formula one racing cars and well-loved brands like Woolworths, can get tired. Software companies make their money by inventing better software and, in fairness, technology available today probably wasn’t even thought of five years ago. Businesses would do well to know what software they use, when it is due to expire and what risks they carry. Plan to replace software and hardware rather than ignore the issue because once software expires it no longer receives security patches and updates. Microsoft is still saying that Windows 7 will expire in January 2020. What’s your plan?
Apply Software Updates
All software needs patches and updates. Anti-virus software needs updating when new threats and antidotes are discovered. Meanwhile software suppliers frequently update their software to fix bugs and oddities and to fix any security issues that have been discovered. “Patch Tuesday” is the name given to the day each month that Microsoft release security and other patches for their software. Ideally patches and updates should be applied automatically but it is amazing how many organisations don’t do this. The updates are available free of charge but simply haven’t been applied. A popular cause is PCs are switched off every night and the automatic update hasn’t been configured.
User Training
Employees are often the weakest link in your Cyber security and data protection. Many companies who use Office 365 for email have neglected to change the settings to prevent staff setting up work email on their personal devices. Is it ok when work email is on the home iPad or Tablet and the family can read it? Would the employee notify you if the device was stolen and other people could read their work email?
Hackers are finding firewalls difficult to circumvent so are resorting to links within emails that, once activated, insert a Trojan or maybe simply encrypt all of your files and ask for a ransom. If you received an email from a parcel company saying that they “couldn’t deliver and click this link to arrange collection” what would you do? Director scam-emails targeting SMEs are also on the rise and appear to work. Not that long ago a property sector company was duped out of £102,000 by a supposed supplier email advising them of a change of bank details. The money was sent to the new account but a week later the genuine supplier called to ask for their money. Only then did the fraud finally came to light.
Train your staff and make sure you have the necessary policies and procedures in place.
Have a Plan & Test It
Would you know what to do if you had a Cyber incident? Are you aware of your obligation to report to the Information Commissioner’s Office (ICO) with 72 hours and would you know what information they expect? Our experience is that few companies have a plan in place and many small and medium businesses would not know what to do if their key IT individual was unobtainable due to holiday or illness.
A confident director would know the answer to this question: if our IT was compromised or ceased to function, how quickly could we get our key systems working again? The two secondary questions are “what would the impact be on our business” and “what would we need to tell the ICO?”
Get on Board with Cyber-Essentials
There is no one single product that will provide a complete guarantee of your cyber-security. We recommend looking at the Cyber-Essentials and Cyber-Essentials Plus schemes, specifically designed for SME business. Cyber-essentials aim is to establish the security controls & ongoing support needed, including five key controls for keeping your data / information secure. Obtaining a Cyber Essentials certificate can provide certain security assurances and help protect personal data in your IT systems.[i]
Cyber Attacks Products & Services
Introduction
So far, we have identified some of the potential issues and looked at some best practices. However, you may not be able to do some of these things yet. If this were your health, we might advise you to eat five veg a day, take regular cardio vascular exercise and smile a lot, all of which you have to do yourself. Thankfully IT is quite different; you don’t have to do it all yourself and Charlton Networks can help you combat these cyber threats with a mix of products, services and solutions. We also recommend taking a look at our guide on effective IT Risk Management.
At Charlton Networks we provide many products and services that work for your business. For IT departments we help set up essential cyber security products for monitoring, protection and recovery. You can also opt for a full cyber security managed service where we take care of everything, leaving your IT free to concentrate on other areas of the business.
The following list gives you an overview of technology products & services that can be used to improve cyber-security to SME businesses and all are provided by Charlton Networks.
Cyber-Security Glossary
2 Factor Authentication:
Provides a two-part login process to computer networks or online web-based systems. This is an additional layer of security that requires a valid user name, a current password and a one-time password, provided to the user during the login process. This is known as multi factor authentication which provides this one-time password via a code, typically supplied via SMS to the user’s mobile phone. This may also take the form of a token ID or dongle, which is in the user’s possession and which is constantly changing.
Active Directory (AD):
Is the system used by Microsoft, used on Windows domains and networks and controls the user log-on to the system and ensures passwords are sufficient strength and changed on a periodic basis. Most companies would have a password policy, which is reflected in the AD password management set-up.
Backup:
The ultimate protection against a cyber-attach, especially something like the crypto-locker malware infection, is the backup of your systems. We recommend using Altaro for your physical / virtual servers or machines and for your Office365 backup too. Having a tried and tested disaster recovery solution, means having the ability to recover when things go wrong. Backups should be fully encrypted and managed from anywhere on a daily basis by your IT provider. But also remember that ‘blended’ attacks involving both automated programs and real people are increasing and their sophistication growing. This means that is your backups are connected to your network they can be vulnerable. Therefore, always consider heavily restricting access, having multiple copies of backups and having off-site or cloud backup copies as the ultimate protection in the event of a malware infection.
Bring Your Own Device / BYOD:
Bring your own device (BYOD) relates to the policy of allowing company employees to bring personally owned devices (laptops, tablets, and smart phones) to their workplace and use these devices to access company systems and company data. This sounds great, making employees and employers lives easier, but just watch out for the potential cyber-security and data security issues. Think about how devices can be controlled and where risks can be minimised. BYOD is often best used with Internet based web applications.
Digital Certificates:
SSL certificates ensure that your company is following good digital data security and is encrypting the communication between the end user and the application. SSL certificates are used for your web sites & web servers, to secure your remote access and secure credit card transactions. Most web browsers now alert if web browsing is not done via secure SSL connection and make sure your certificates are managed and renewed.
Endpoint Protection:
This is a catch-all terms often used to describe the anti-virus / anti-malware software that runs on Windows, Android or Apple devices. Endpoint protection can include signature based anti-virus (preventing known viruses and malware), content management (preventing access to rouge websites) and increasingly AI intelligence-based protection covers unknown vulnerabilities. This later area is based on software recognising unusual behaviour and preventing operation and is found in leading products, such as Sophos Intercept-X[ii].
Anti-spam:
Business users rely upon their email and its constant use. Look for systems that blocks spam in the cloud before it reaches your site or at the least have gateway anti-spam that blocks it before entering your network. In this way, removing spam decreases the risk of end users receiving malicious viruses and spam, but also reduced the workload of your computers, saving energy and making systems faster.
Antispyware:
Spyware typically installs itself on to your computer, without your knowledge or permission. Spyware then sends information from your computer to a third party, possibly as a way of gaining ‘social information’ about you the user. This is then used to engineer attacks against the individual or the company. Look for products like Sophos that are 100% Check mark-certified for spyware detection.
Content Filtering:
Content-filtering controls and filters Internet access and website content, preventing access to black-listed sites or those known to be sources on viruses and malware.
For SME business. Content filtering can be deployed as part of a firewall or unified threat management (UTM) solution or as a dedicated web filtering appliance.
Employee Cyber Security Awareness:
Increasingly cyber-security is about the employee awareness, as well as the technical systems that are deployed. This involves user training, user awareness and monitoring of users behaviour. The purpose is to reduce risk by helping employees & users to become better informed about security threats, more sceptical about what they receive and less likely to commit damaging behaviours like clicking on malicious links in email, sharing on social media, or taking risks through other electronic channels.
Firewall:
Hardware or software-based firewall systems provide the connection to the Internet and protect all devices that sit on your networks. These firewalls devices provide filtering and blocking of unwanted data and connections, they provide visibility of your network, users, and applications being used control who can access what. Increasingly, Unified Threat Management units now provide a range of functions that include firewall stateful packet inspection.
Unified Threat Management / UTM:
A unified threat management device combines hardware and software to provides a number of security functions in a single unit. For example, the Sophos UTM, provides firewall, content filtering, IPS, anti-virus gateway and many more functions in a single device. This gives SMEs greater functionality for the cost and makes management and operation easier.
Incident Response Plan:
An action plan that covers the immediate response / actions an organisation will take in the event of a cyber-attack or other serious incident. Charlton Networks help SME companies develop incident response plans for cyber or other disaster recovery scenarios.
Intrusion Detection (IDS) / Prevention Services (IPS):
IDS and IPS monitor network access at the firewall / UTM gateway and detects anomalies in traffic by looking for unusual patterns of network activity. These patterns are associated with misuse of the IT systems and aim to catch bad behaviour, such as multiple login attempts and other known attack scenarios from internal or external network sources. IPS goes a step further and shuts down these activities by blocking the traffic sources and stopping the misuse automatically.
Risk Analysis:
A risk analysis systematically identifies critical system resources and threats, quantifying potential impacts / losses of productivity and recommends how to mitigate such risks via a range of countermeasures to eliminate or minimize exposure.
Security Policy:
Charlton Networks helps companies create a set of policies and practices that describe how an organization manages, protects, and distributes its sensitive company information.
Vulnerability Scanning:
An Automated testing regime that reviews computer devices, PCs, servers, networks and other network attached devices for the existence of potential cyber-vulnerabilities or known-exploits that might allow cyber criminals to gain access to a computer system. Operated on a regular basis, vulnerability scanning tests every device connected to your network(s), generating a report of the most important issues and problems
Remote Management & Monitoring (RMM)
RMM tools are designed to managed the complex IT environment, including the proactive monitoring of devices and their security patching. Proactively managing devices, ensuring all applications are patched and vulnerabilities removed is a major step toward securing your business IT environment.
Some Key Cyber-Security Stats for SMEs
Here are some figures to backup the information provided so far;
- 90% of SME’s feel they will struggle against malware over the coming 12-months.
- 92% of SME’s consider ransomware a major threat over the next 12-months.
- IT Managers spend 25% of their time on average, managing security solutions.
- Almost half of IT Managers work more than their contracted hours due to security related problems.
- 69% of IT Managers use multiple consoles to manage their organisations AV, where 73% say they would prefer a single portal to use.
- 60% of IT Managers would prefer one single vendor if it reduces the management time and improves security. (source: Sophos[iii])
Further Reading
Here are some further links to useful sites and publications that can provide more detail on cyber-security issues, risks and ways to avoid problems. We hope you have found this guide useful and if you’d like more details then please contact us and we’d be delighted to help;
- 2018 Technology Industry Outlook – Deloitte – https://www2.deloitte.com/us/en/pages/technology-media-and-telecommunications/articles/technology-industry-outlook.html
- A Practical Guide to IT Security – Information Commissioners Office – https://ico.org.uk/media/for-organisations/documents/1575/it_security_practical_guide.pdf
- Cyber security for your organisation starts here – NCSC https://www.cyberessentials.ncsc.gov.uk/advice/
- Worse Passwords of 2022
- Cyber-security system buyers guide – Sophos
- 7-uncomfortable truths of EndPoint Security – Sophos – https://secure2.sophos.com/en-us/security-news-trends/whitepapers/gated-wp/uncomfortable-truths-of-endpoint-security.aspx
[i] https://www.cyberessentials.ncsc.gov.uk/
[ii] https://www.charltonnetworks.co.uk/charlton-networks-products/sophos-cyber-security/
[iii] Source – Sophos “IT SECURITY SMALL BUSINESS SURVEY, 2018”
Stay Connected
Subscribe for monthly tips and resources on how to transform your business through technology.
Business Resources
What is an IT Audit?
The Ultimate Guide to Effective IT Risk Management
6 Business Technology Challenges for 2022
Protect Your Business from Cyber Attacks
Outsourcing your IT services means you get access to a team of IT experts available when you need it most.

IT Consultancy
Our IT Consultancy services cover a wider range of Business IT topics, that include cyber-security. Good cyber-security starts by reviewing your current set-up, understanding your current risks and building a plan to fix these gaps.
We bring many years of experience and offer a FREE Network Audit, that can be focused upon cyber-security to get you started.

IT Security Solutions
We sell and support a range of network & IT security solutions to keep your business secure on-line.
Our project team install, set-up and manage IT projects for a range of cyber-security solutions. We complete network upgrades, integrate systems or replace old network infrastructure hardware & software.
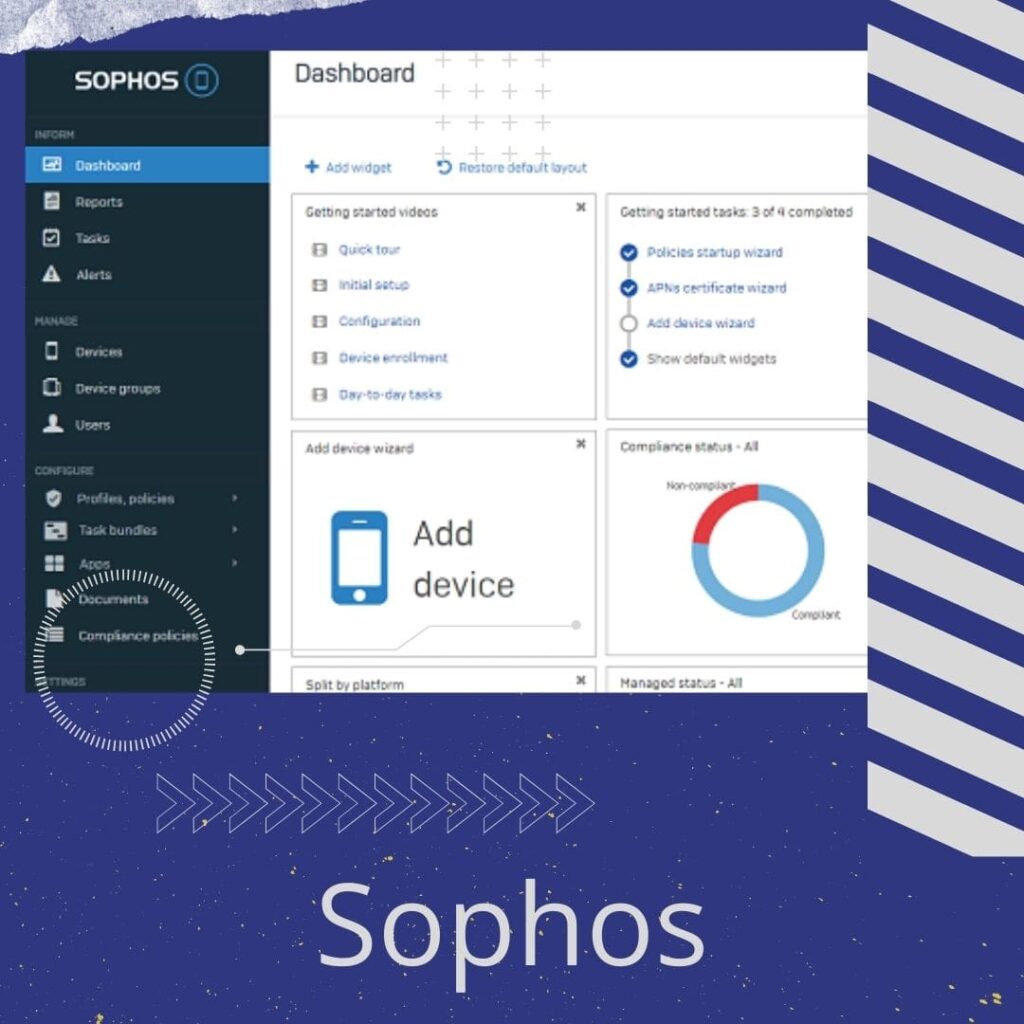
SOPHOS
Charlton Network and Sophos have a 20+ year partnership, that recognises us as a Gold Partner. This means we have attained the highest levels of accreditation and are able to specifiy, supply, install and support all Sophos products & services.
Sophos provides leading cyber-security solutions for business users. From Email, device & server protection, through to advance detection & 24*7 threat hunting.
Discover how we can help. Contact us today!



